|
市場調査レポート
商品コード
1298203
自動BAS(Breach and Attack Simulation)市場:提供別、展開モード別、用途別、エンドユーザー別:世界の機会分析と産業予測、2021-2031年Automated Breach and Attack Simulation Market By Offering, By Deployment Mode, By Application, By End User : Global Opportunity Analysis and Industry Forecast, 2021-2031 |
||||||
| 自動BAS(Breach and Attack Simulation)市場:提供別、展開モード別、用途別、エンドユーザー別:世界の機会分析と産業予測、2021-2031年 |
|
出版日: 2023年03月01日
発行: Allied Market Research
ページ情報: 英文 426 Pages
納期: 2~3営業日
|
- 全表示
- 概要
- 図表
- 目次
自動BAS(Breach and Attack Simulation)は、高度なコンピューターセキュリティテスト手法の一種です。
悪意のある行為者が使用しそうな攻撃経路や攻撃手法をシミュレートすることで、セキュリティ環境のさまざまな脆弱性を特定することを目的としています。加えて、組織が自社のセキュリティ管理体制を評価し、サイバー脅威を検知・軽減する能力を評価することも可能にします。さらに、組織がシステムの能力を測定、管理、改善し、サイバー攻撃から効果的に防御するのに役立つ重要な洞察を提供します。自動BASはまた、組織が潜在的な脆弱性やその他の問題を早期に特定することを可能にします。
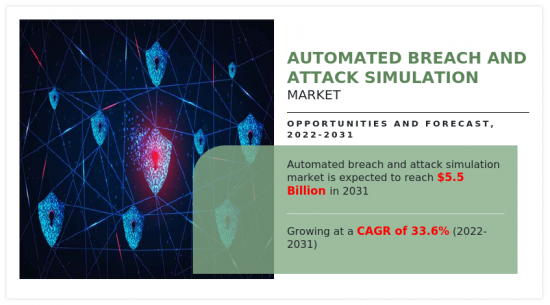
セキュリティ脅威の管理が複雑化し、セキュリティ投資の優先順位付けに対する要求が高まっていることが、世界の自動BAS(Breach and Attack Simulation)市場の成長を後押ししています。また、世界中でサイバー攻撃が増加していることが、自動BAS(Breach and Attack Simulation)市場の成長にプラスの影響を与えています。しかし、熟練したセキュリティ専門家の不足と高度なサイバーセキュリティ技術に関する認識不足が、自動BAS(Breach and Attack Simulation)市場の成長を妨げています。これとは逆に、デジタル化イニシアチブの台頭は、予測期間中、自動BAS(Breach and Attack Simulation)市場の拡大に有益な機会を提供すると期待されています。
目次
第1章 イントロダクション
第2章 エグゼクティブサマリー
第3章 市場概要
- 市場の定義と範囲
- 主な調査結果
- 影響要因
- 主な投資ポケット
- ポーターのファイブフォース分析
- 供給企業の交渉力
- 買い手の交渉力
- 代替品の脅威
- 新規参入業者の脅威
- 競合の激しさ
- 市場力学
- 促進要因
- セキュリティ脅威管理の複雑化
- セキュリティ投資の優先順位付けに対する需要の増加
- 世界のサイバー攻撃の増加
- 阻害要因
- 熟練したセキュリティ専門家の不足
- 高度なサイバーセキュリティ技術に関する認識不足
- 機会
- デジタル化への取り組みの増加
- 促進要因
- COVID-19:市場への影響分析
第4章 自動BAS(Breach and Attack Simulation)市場:提供別
- 概要
- 市場規模と予測
- プラットフォーム・ツール
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
- サービス
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
第5章 自動BAS(Breach and Attack Simulation)市場:展開モード別
- 概要
- 市場規模と予測
- オンプレミス
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
- クラウド
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
第6章 自動BAS(Breach and Attack Simulation)市場:用途別
- 概要
- 市場規模と予測
- 構成管理
- 主要市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
- パッチ管理
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
- 脅威管理
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
- その他
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
第7章 自動BAS(Breach and Attack Simulation)市場:エンドユーザー別
- 概要
- 市場規模と予測
- エンタープライズ・データセンター
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
- マネージドサービスプロバイダー
- 主な市場動向、成長要因、機会
- 市場規模・予測:地域別
- 市場シェア分析:国別
第8章 自動BAS(Breach and Attack Simulation)市場:地域別
- 概要
- 市場規模・予測:地域別
- 北米
- 主な動向と機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 市場規模・予測:国別
- 米国
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- カナダ
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 欧州
- 主な動向と機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 市場規模・予測:国別
- 英国
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- ドイツ
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- フランス
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- イタリア
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- スペイン
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- その他欧州
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- アジア太平洋地域
- 主な動向と機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 市場規模・予測:国別
- 中国
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 日本
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- インド市場
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- オーストラリア
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 韓国
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- その他アジア太平洋地域
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- ラテンアメリカ・中東・アフリカ
- 主な動向と機会
- 市場規模・予測:提供別
- 市場規模・予測:展開モード別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 市場規模・予測:国別
- ラテンアメリカ
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- 中東
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
- アフリカ市場
- 主要市場動向、成長要因、機会
- 市場規模・予測:提供別
- 市場規模・予測:展開形態別
- 市場規模・予測:用途別
- 市場規模・予測:エンドユーザー別
第9章 競合情勢
- イントロダクション
- 主要成功戦略
- 主要10社の製品マッピング
- 競合ダッシュボード
- 競合ヒートマップ
- トップ企業のポジショニング(2021年
第10章 企業プロファイル
- AttackIQ.
- Cymulate.
- FireMon, LLC.
- Keysight Technologies
- Qualys, Inc.
- Rapid7
- SafeBreach Inc.
- Skybox Security, Inc.
- Sophos Ltd.
- XM Cyber
LIST OF TABLES
- TABLE 01. GLOBAL AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 02. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR PLATFORMS AND TOOLS, BY REGION, 2021-2031 ($MILLION)
- TABLE 03. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR SERVICES, BY REGION, 2021-2031 ($MILLION)
- TABLE 04. GLOBAL AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 05. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR ON-PREMISES, BY REGION, 2021-2031 ($MILLION)
- TABLE 06. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR CLOUD, BY REGION, 2021-2031 ($MILLION)
- TABLE 07. GLOBAL AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 08. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR CONFIGURATION MANAGEMENT, BY REGION, 2021-2031 ($MILLION)
- TABLE 09. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR PATCH MANAGEMENT, BY REGION, 2021-2031 ($MILLION)
- TABLE 10. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR THREAT MANAGEMENT, BY REGION, 2021-2031 ($MILLION)
- TABLE 11. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR OTHERS, BY REGION, 2021-2031 ($MILLION)
- TABLE 12. GLOBAL AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 13. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR ENTERPRISES AND DATA CENTERS, BY REGION, 2021-2031 ($MILLION)
- TABLE 14. AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR MANAGED SERVICE PROVIDERS, BY REGION, 2021-2031 ($MILLION)
- TABLE 15. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY REGION, 2021-2031 ($MILLION)
- TABLE 16. NORTH AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 17. NORTH AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 18. NORTH AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 19. NORTH AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 20. NORTH AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY COUNTRY, 2021-2031 ($MILLION)
- TABLE 21. U.S. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 22. U.S. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 23. U.S. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 24. U.S. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 25. CANADA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 26. CANADA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 27. CANADA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 28. CANADA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 29. EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 30. EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 31. EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 32. EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 33. EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY COUNTRY, 2021-2031 ($MILLION)
- TABLE 34. UK AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 35. UK AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 36. UK AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 37. UK AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 38. GERMANY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 39. GERMANY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 40. GERMANY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 41. GERMANY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 42. FRANCE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 43. FRANCE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 44. FRANCE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 45. FRANCE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 46. ITALY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 47. ITALY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 48. ITALY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 49. ITALY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 50. SPAIN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 51. SPAIN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 52. SPAIN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 53. SPAIN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 54. REST OF EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 55. REST OF EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 56. REST OF EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 57. REST OF EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 58. ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 59. ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 60. ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 61. ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 62. ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY COUNTRY, 2021-2031 ($MILLION)
- TABLE 63. CHINA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 64. CHINA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 65. CHINA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 66. CHINA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 67. JAPAN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 68. JAPAN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 69. JAPAN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 70. JAPAN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 71. INDIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 72. INDIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 73. INDIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 74. INDIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 75. AUSTRALIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 76. AUSTRALIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 77. AUSTRALIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 78. AUSTRALIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 79. SOUTH KOREA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 80. SOUTH KOREA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 81. SOUTH KOREA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 82. SOUTH KOREA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 83. REST OF ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 84. REST OF ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 85. REST OF ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 86. REST OF ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 87. LAMEA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 88. LAMEA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 89. LAMEA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 90. LAMEA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 91. LAMEA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY COUNTRY, 2021-2031 ($MILLION)
- TABLE 92. LATIN AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 93. LATIN AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 94. LATIN AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 95. LATIN AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 96. MIDDLE EAST AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 97. MIDDLE EAST AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 98. MIDDLE EAST AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 99. MIDDLE EAST AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 100. AFRICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021-2031 ($MILLION)
- TABLE 101. AFRICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021-2031 ($MILLION)
- TABLE 102. AFRICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021-2031 ($MILLION)
- TABLE 103. AFRICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021-2031 ($MILLION)
- TABLE 104. ATTACKIQ.: KEY EXECUTIVES
- TABLE 105. ATTACKIQ.: COMPANY SNAPSHOT
- TABLE 106. ATTACKIQ.: PRODUCT SEGMENTS
- TABLE 107. ATTACKIQ.: PRODUCT PORTFOLIO
- TABLE 108. ATTACKIQ.: KEY STRATERGIES
- TABLE 109. CYMULATE.: KEY EXECUTIVES
- TABLE 110. CYMULATE.: COMPANY SNAPSHOT
- TABLE 111. CYMULATE.: PRODUCT SEGMENTS
- TABLE 112. CYMULATE.: PRODUCT PORTFOLIO
- TABLE 113. CYMULATE.: KEY STRATERGIES
- TABLE 114. FIREMON, LLC.: KEY EXECUTIVES
- TABLE 115. FIREMON, LLC.: COMPANY SNAPSHOT
- TABLE 116. FIREMON, LLC.: PRODUCT SEGMENTS
- TABLE 117. FIREMON, LLC.: PRODUCT PORTFOLIO
- TABLE 118. FIREMON, LLC.: KEY STRATERGIES
- TABLE 119. KEYSIGHT TECHNOLOGIES: KEY EXECUTIVES
- TABLE 120. KEYSIGHT TECHNOLOGIES: COMPANY SNAPSHOT
- TABLE 121. KEYSIGHT TECHNOLOGIES: PRODUCT SEGMENTS
- TABLE 122. KEYSIGHT TECHNOLOGIES: PRODUCT PORTFOLIO
- TABLE 123. KEYSIGHT TECHNOLOGIES: KEY STRATERGIES
- TABLE 124. QUALYS, INC.: KEY EXECUTIVES
- TABLE 125. QUALYS, INC.: COMPANY SNAPSHOT
- TABLE 126. QUALYS, INC.: PRODUCT SEGMENTS
- TABLE 127. QUALYS, INC.: PRODUCT PORTFOLIO
- TABLE 128. QUALYS, INC.: KEY STRATERGIES
- TABLE 129. RAPID7: KEY EXECUTIVES
- TABLE 130. RAPID7: COMPANY SNAPSHOT
- TABLE 131. RAPID7: PRODUCT SEGMENTS
- TABLE 132. RAPID7: PRODUCT PORTFOLIO
- TABLE 133. RAPID7: KEY STRATERGIES
- TABLE 134. SAFEBREACH INC.: KEY EXECUTIVES
- TABLE 135. SAFEBREACH INC.: COMPANY SNAPSHOT
- TABLE 136. SAFEBREACH INC.: PRODUCT SEGMENTS
- TABLE 137. SAFEBREACH INC.: PRODUCT PORTFOLIO
- TABLE 138. SAFEBREACH INC.: KEY STRATERGIES
- TABLE 139. SKYBOX SECURITY, INC.: KEY EXECUTIVES
- TABLE 140. SKYBOX SECURITY, INC.: COMPANY SNAPSHOT
- TABLE 141. SKYBOX SECURITY, INC.: PRODUCT SEGMENTS
- TABLE 142. SKYBOX SECURITY, INC.: PRODUCT PORTFOLIO
- TABLE 143. SKYBOX SECURITY, INC.: KEY STRATERGIES
- TABLE 144. SOPHOS LTD.: KEY EXECUTIVES
- TABLE 145. SOPHOS LTD.: COMPANY SNAPSHOT
- TABLE 146. SOPHOS LTD.: SERVICE SEGMENTS
- TABLE 147. SOPHOS LTD.: PRODUCT PORTFOLIO
- TABLE 148. SOPHOS LTD.: KEY STRATERGIES
- TABLE 149. XM CYBER: KEY EXECUTIVES
- TABLE 150. XM CYBER: COMPANY SNAPSHOT
- TABLE 151. XM CYBER: PRODUCT SEGMENTS
- TABLE 152. XM CYBER: PRODUCT PORTFOLIO
LIST OF FIGURES
- FIGURE 01. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031
- FIGURE 02. SEGMENTATION OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031
- FIGURE 03. TOP INVESTMENT POCKETS IN AUTOMATED BREACH AND ATTACK SIMULATION MARKET (2022-2031)
- FIGURE 04. LOW BARGAINING POWER OF SUPPLIERS
- FIGURE 05. LOW BARGAINING POWER OF BUYERS
- FIGURE 06. LOW THREAT OF SUBSTITUTES
- FIGURE 07. LOW THREAT OF NEW ENTRANTS
- FIGURE 08. LOW INTENSITY OF RIVALRY
- FIGURE 09. DRIVERS, RESTRAINTS AND OPPORTUNITIES: GLOBALAUTOMATED BREACH AND ATTACK SIMULATION MARKET
- FIGURE 10. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING, 2021(%)
- FIGURE 11. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR PLATFORMS AND TOOLS, BY COUNTRY 2021 AND 2031(%)
- FIGURE 12. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR SERVICES, BY COUNTRY 2021 AND 2031(%)
- FIGURE 13. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE, 2021(%)
- FIGURE 14. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR ON-PREMISES, BY COUNTRY 2021 AND 2031(%)
- FIGURE 15. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR CLOUD, BY COUNTRY 2021 AND 2031(%)
- FIGURE 16. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION, 2021(%)
- FIGURE 17. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR CONFIGURATION MANAGEMENT, BY COUNTRY 2021 AND 2031(%)
- FIGURE 18. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR PATCH MANAGEMENT, BY COUNTRY 2021 AND 2031(%)
- FIGURE 19. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR THREAT MANAGEMENT, BY COUNTRY 2021 AND 2031(%)
- FIGURE 20. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR OTHERS, BY COUNTRY 2021 AND 2031(%)
- FIGURE 21. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER, 2021(%)
- FIGURE 22. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR ENTERPRISES AND DATA CENTERS, BY COUNTRY 2021 AND 2031(%)
- FIGURE 23. COMPARATIVE SHARE ANALYSIS OF AUTOMATED BREACH AND ATTACK SIMULATION MARKET FOR MANAGED SERVICE PROVIDERS, BY COUNTRY 2021 AND 2031(%)
- FIGURE 24. AUTOMATED BREACH AND ATTACK SIMULATION MARKET BY REGION, 2021
- FIGURE 25. U.S. AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 26. CANADA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 27. UK AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 28. GERMANY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 29. FRANCE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 30. ITALY AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 31. SPAIN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 32. REST OF EUROPE AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 33. CHINA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 34. JAPAN AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 35. INDIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 36. AUSTRALIA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 37. SOUTH KOREA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 38. REST OF ASIA-PACIFIC AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 39. LATIN AMERICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 40. MIDDLE EAST AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 41. AFRICA AUTOMATED BREACH AND ATTACK SIMULATION MARKET, 2021-2031 ($MILLION)
- FIGURE 42. TOP WINNING STRATEGIES, BY YEAR
- FIGURE 43. TOP WINNING STRATEGIES, BY DEVELOPMENT
- FIGURE 44. TOP WINNING STRATEGIES, BY COMPANY
- FIGURE 45. PRODUCT MAPPING OF TOP 10 PLAYERS
- FIGURE 46. COMPETITIVE DASHBOARD
- FIGURE 47. COMPETITIVE HEATMAP: AUTOMATED BREACH AND ATTACK SIMULATION MARKET
- FIGURE 48. TOP PLAYER POSITIONING, 2021
- FIGURE 49. KEYSIGHT TECHNOLOGIES: NET REVENUE, 2020-2022 ($MILLION)
- FIGURE 50. KEYSIGHT TECHNOLOGIES: RESEARCH & DEVELOPMENT EXPENDITURE, 2020-2022 ($MILLION)
- FIGURE 51. KEYSIGHT TECHNOLOGIES: REVENUE SHARE BY REGION, 2022 (%)
- FIGURE 52. KEYSIGHT TECHNOLOGIES: REVENUE SHARE BY SEGMENT, 2022 (%)
- FIGURE 53. QUALYS, INC.: NET REVENUE, 2020-2022 ($MILLION)
- FIGURE 54. QUALYS, INC.: RESEARCH & DEVELOPMENT EXPENDITURE, 2020-2022 ($MILLION)
- FIGURE 55. QUALYS, INC.: REVENUE SHARE BY REGION, 2022 (%)
- FIGURE 56. RAPID7: NET REVENUE, 2019-2021 ($MILLION)
- FIGURE 57. RAPID7: RESEARCH & DEVELOPMENT EXPENDITURE, 2019-2021 ($MILLION)
- FIGURE 58. RAPID7: REVENUE SHARE BY REGION, 2021 (%)
- FIGURE 59. RAPID7: REVENUE SHARE BY SEGMENT, 2021 (%)
Automated breach and attack simulation is a type of advanced computer security testing method. It aims to identify different vulnerabilities in security environments by simulating the attack paths and techniques likely to be used by malicious actors. In addition, it allows organizations to evaluate their security controls and their ability to detect and mitigate against cyber threats. Moreover, it provides vital insights to help organization measure, manage and improve the ability of its systems and defend effectively against cyber-attacks. ABAS also enable organization to identify potential vulnerabilities or other issues problems early on. Breach simulations are especially valuable in the face of increasingly complex enterprise networks and the shift towards cloud computing, IoT and remote working.
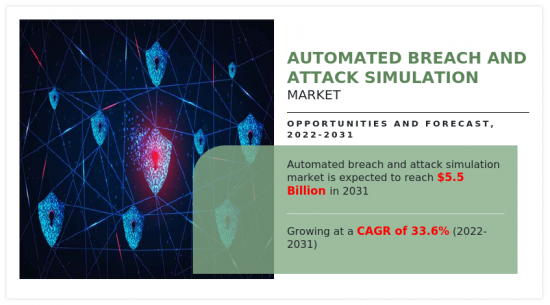
Increase in complexities in managing security threats and increase in demand for Prioritizing Security Investments is boosting the growth of the global automated breach and attack simulation market. In addition, growing number of cyber-attacks across the globe is positively impacting growth of the automated breach and attack simulation market. However, lack of skilled security experts and lack of awareness related to advanced cybersecurity technologies is hampering the automated breach and attack simulation market growth. On the contrary, Rise in digitalization initiatives is expected to offer remunerative opportunities for expansion of the automated breach and attack simulation market during the forecast period.
The automated breach and attack simulation market is segmented on the basis of by offering, deployment mode, application, end-user, and region. On the basis of offering, the market is categorized into platform and tools, and service. On the basis of deployment mode, the market is fragmented into on-premise, and cloud. On the basis of application, the market is bifurcated into configuration management, patch management, threat management, and others. By end-user, it is classified into enterprise and data centers, and managed service providers. By region, the market is analyzed across North America, Europe, Asia-Pacific, and LAMEA.
The key players that operate in the automated breach and attack simulation market are: AttackIQ, Keysight Technologies, Qualys, Inc., Rapid7, Sophos Ltd., Cymulate, FireMon, LLC., SafeBreach Inc., Skybox Security, Inc, Skybox Security, Inc, and XM Cyber. These players have adopted various strategies to increase their market penetration and strengthen their position in the industry.
KEY BENEFITS FOR STAKEHOLDERS
- The study provides an in-depth analysis of the global automated breach and attack simulation market forecast along with the current and future trends to explain the imminent investment pockets.
- Information about key drivers, restraints, and opportunities and their impact analysis on global automated breach and attack simulation market trend is provided in the report.
- The Porter's five forces analysis illustrates the potency of the buyers and suppliers operating in the industry.
- The quantitative analysis of the market from 2022 to 2031 is provided to determine the market potential.
Key Market Segments
By Offering
- Platforms and Tools
- Services
By Deployment Mode
- On-Premises
- Cloud
By Application
- Configuration Management
- Patch Management
- Threat Management
- Others
By End User
- Enterprises and Data Centers
- Managed Service Providers
By Region
- North America
- U.S.
- Canada
- Europe
- UK
- Germany
- France
- Italy
- Spain
- Rest of Europe
- Asia-Pacific
- China
- Japan
- India
- Australia
- South Korea
- Rest of Asia-Pacific
- LAMEA
- Latin America
- Middle East
- Africa
Key Market Players:
- AttackIQ.
- Keysight Technologies
- Qualys, Inc.
- Rapid7
- Sophos Ltd.
- Cymulate.
- FireMon, LLC.
- SafeBreach Inc.
- Skybox Security, Inc.
- XM Cyber
TABLE OF CONTENTS
CHAPTER 1: INTRODUCTION
- 1.1. Report description
- 1.2. Key market segments
- 1.3. Key benefits to the stakeholders
- 1.4. Research Methodology
- 1.4.1. Primary research
- 1.4.2. Secondary research
- 1.4.3. Analyst tools and models
CHAPTER 2: EXECUTIVE SUMMARY
- 2.1. CXO Perspective
CHAPTER 3: MARKET OVERVIEW
- 3.1. Market definition and scope
- 3.2. Key findings
- 3.2.1. Top impacting factors
- 3.2.2. Top investment pockets
- 3.3. Porter's five forces analysis
- 3.3.1. Bargaining power of suppliers
- 3.3.2. Bargaining power of buyers
- 3.3.3. Threat of substitutes
- 3.3.4. Threat of new entrants
- 3.3.5. Intensity of rivalry
- 3.4. Market dynamics
- 3.4.1. Drivers
- 3.4.1.1. Increase in complexities in managing security threats
- 3.4.1.2. Increase in demand for Prioritizing Security Investments
- 3.4.1.3. Growing number of cyber-attacks across the globe
- 3.4.1. Drivers
- 3.4.2. Restraints
- 3.4.2.1. Lack of skilled security experts
- 3.4.2.2. Lack of awareness related to advanced cybersecurity technologies
- 3.4.3. Opportunities
- 3.4.3.1. Rise in digitalization initiatives
- 3.5. COVID-19 Impact Analysis on the market
CHAPTER 4: AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY OFFERING
- 4.1. Overview
- 4.1.1. Market size and forecast
- 4.2. Platforms and Tools
- 4.2.1. Key market trends, growth factors and opportunities
- 4.2.2. Market size and forecast, by region
- 4.2.3. Market share analysis by country
- 4.3. Services
- 4.3.1. Key market trends, growth factors and opportunities
- 4.3.2. Market size and forecast, by region
- 4.3.3. Market share analysis by country
CHAPTER 5: AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY DEPLOYMENT MODE
- 5.1. Overview
- 5.1.1. Market size and forecast
- 5.2. On-Premises
- 5.2.1. Key market trends, growth factors and opportunities
- 5.2.2. Market size and forecast, by region
- 5.2.3. Market share analysis by country
- 5.3. Cloud
- 5.3.1. Key market trends, growth factors and opportunities
- 5.3.2. Market size and forecast, by region
- 5.3.3. Market share analysis by country
CHAPTER 6: AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY APPLICATION
- 6.1. Overview
- 6.1.1. Market size and forecast
- 6.2. Configuration Management
- 6.2.1. Key market trends, growth factors and opportunities
- 6.2.2. Market size and forecast, by region
- 6.2.3. Market share analysis by country
- 6.3. Patch Management
- 6.3.1. Key market trends, growth factors and opportunities
- 6.3.2. Market size and forecast, by region
- 6.3.3. Market share analysis by country
- 6.4. Threat Management
- 6.4.1. Key market trends, growth factors and opportunities
- 6.4.2. Market size and forecast, by region
- 6.4.3. Market share analysis by country
- 6.5. Others
- 6.5.1. Key market trends, growth factors and opportunities
- 6.5.2. Market size and forecast, by region
- 6.5.3. Market share analysis by country
CHAPTER 7: AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY END USER
- 7.1. Overview
- 7.1.1. Market size and forecast
- 7.2. Enterprises and Data Centers
- 7.2.1. Key market trends, growth factors and opportunities
- 7.2.2. Market size and forecast, by region
- 7.2.3. Market share analysis by country
- 7.3. Managed Service Providers
- 7.3.1. Key market trends, growth factors and opportunities
- 7.3.2. Market size and forecast, by region
- 7.3.3. Market share analysis by country
CHAPTER 8: AUTOMATED BREACH AND ATTACK SIMULATION MARKET, BY REGION
- 8.1. Overview
- 8.1.1. Market size and forecast By Region
- 8.2. North America
- 8.2.1. Key trends and opportunities
- 8.2.2. Market size and forecast, by Offering
- 8.2.3. Market size and forecast, by Deployment Mode
- 8.2.4. Market size and forecast, by Application
- 8.2.5. Market size and forecast, by End User
- 8.2.6. Market size and forecast, by country
- 8.2.6.1. U.S.
- 8.2.6.1.1. Key market trends, growth factors and opportunities
- 8.2.6.1.2. Market size and forecast, by Offering
- 8.2.6.1.3. Market size and forecast, by Deployment Mode
- 8.2.6.1.4. Market size and forecast, by Application
- 8.2.6.1.5. Market size and forecast, by End User
- 8.2.6.2. Canada
- 8.2.6.2.1. Key market trends, growth factors and opportunities
- 8.2.6.2.2. Market size and forecast, by Offering
- 8.2.6.2.3. Market size and forecast, by Deployment Mode
- 8.2.6.2.4. Market size and forecast, by Application
- 8.2.6.2.5. Market size and forecast, by End User
- 8.3. Europe
- 8.3.1. Key trends and opportunities
- 8.3.2. Market size and forecast, by Offering
- 8.3.3. Market size and forecast, by Deployment Mode
- 8.3.4. Market size and forecast, by Application
- 8.3.5. Market size and forecast, by End User
- 8.3.6. Market size and forecast, by country
- 8.3.6.1. UK
- 8.3.6.1.1. Key market trends, growth factors and opportunities
- 8.3.6.1.2. Market size and forecast, by Offering
- 8.3.6.1.3. Market size and forecast, by Deployment Mode
- 8.3.6.1.4. Market size and forecast, by Application
- 8.3.6.1.5. Market size and forecast, by End User
- 8.3.6.2. Germany
- 8.3.6.2.1. Key market trends, growth factors and opportunities
- 8.3.6.2.2. Market size and forecast, by Offering
- 8.3.6.2.3. Market size and forecast, by Deployment Mode
- 8.3.6.2.4. Market size and forecast, by Application
- 8.3.6.2.5. Market size and forecast, by End User
- 8.3.6.3. France
- 8.3.6.3.1. Key market trends, growth factors and opportunities
- 8.3.6.3.2. Market size and forecast, by Offering
- 8.3.6.3.3. Market size and forecast, by Deployment Mode
- 8.3.6.3.4. Market size and forecast, by Application
- 8.3.6.3.5. Market size and forecast, by End User
- 8.3.6.4. Italy
- 8.3.6.4.1. Key market trends, growth factors and opportunities
- 8.3.6.4.2. Market size and forecast, by Offering
- 8.3.6.4.3. Market size and forecast, by Deployment Mode
- 8.3.6.4.4. Market size and forecast, by Application
- 8.3.6.4.5. Market size and forecast, by End User
- 8.3.6.5. Spain
- 8.3.6.5.1. Key market trends, growth factors and opportunities
- 8.3.6.5.2. Market size and forecast, by Offering
- 8.3.6.5.3. Market size and forecast, by Deployment Mode
- 8.3.6.5.4. Market size and forecast, by Application
- 8.3.6.5.5. Market size and forecast, by End User
- 8.3.6.6. Rest of Europe
- 8.3.6.6.1. Key market trends, growth factors and opportunities
- 8.3.6.6.2. Market size and forecast, by Offering
- 8.3.6.6.3. Market size and forecast, by Deployment Mode
- 8.3.6.6.4. Market size and forecast, by Application
- 8.3.6.6.5. Market size and forecast, by End User
- 8.4. Asia-Pacific
- 8.4.1. Key trends and opportunities
- 8.4.2. Market size and forecast, by Offering
- 8.4.3. Market size and forecast, by Deployment Mode
- 8.4.4. Market size and forecast, by Application
- 8.4.5. Market size and forecast, by End User
- 8.4.6. Market size and forecast, by country
- 8.4.6.1. China
- 8.4.6.1.1. Key market trends, growth factors and opportunities
- 8.4.6.1.2. Market size and forecast, by Offering
- 8.4.6.1.3. Market size and forecast, by Deployment Mode
- 8.4.6.1.4. Market size and forecast, by Application
- 8.4.6.1.5. Market size and forecast, by End User
- 8.4.6.2. Japan
- 8.4.6.2.1. Key market trends, growth factors and opportunities
- 8.4.6.2.2. Market size and forecast, by Offering
- 8.4.6.2.3. Market size and forecast, by Deployment Mode
- 8.4.6.2.4. Market size and forecast, by Application
- 8.4.6.2.5. Market size and forecast, by End User
- 8.4.6.3. India
- 8.4.6.3.1. Key market trends, growth factors and opportunities
- 8.4.6.3.2. Market size and forecast, by Offering
- 8.4.6.3.3. Market size and forecast, by Deployment Mode
- 8.4.6.3.4. Market size and forecast, by Application
- 8.4.6.3.5. Market size and forecast, by End User
- 8.4.6.4. Australia
- 8.4.6.4.1. Key market trends, growth factors and opportunities
- 8.4.6.4.2. Market size and forecast, by Offering
- 8.4.6.4.3. Market size and forecast, by Deployment Mode
- 8.4.6.4.4. Market size and forecast, by Application
- 8.4.6.4.5. Market size and forecast, by End User
- 8.4.6.5. South Korea
- 8.4.6.5.1. Key market trends, growth factors and opportunities
- 8.4.6.5.2. Market size and forecast, by Offering
- 8.4.6.5.3. Market size and forecast, by Deployment Mode
- 8.4.6.5.4. Market size and forecast, by Application
- 8.4.6.5.5. Market size and forecast, by End User
- 8.4.6.6. Rest of Asia-Pacific
- 8.4.6.6.1. Key market trends, growth factors and opportunities
- 8.4.6.6.2. Market size and forecast, by Offering
- 8.4.6.6.3. Market size and forecast, by Deployment Mode
- 8.4.6.6.4. Market size and forecast, by Application
- 8.4.6.6.5. Market size and forecast, by End User
- 8.5. LAMEA
- 8.5.1. Key trends and opportunities
- 8.5.2. Market size and forecast, by Offering
- 8.5.3. Market size and forecast, by Deployment Mode
- 8.5.4. Market size and forecast, by Application
- 8.5.5. Market size and forecast, by End User
- 8.5.6. Market size and forecast, by country
- 8.5.6.1. Latin America
- 8.5.6.1.1. Key market trends, growth factors and opportunities
- 8.5.6.1.2. Market size and forecast, by Offering
- 8.5.6.1.3. Market size and forecast, by Deployment Mode
- 8.5.6.1.4. Market size and forecast, by Application
- 8.5.6.1.5. Market size and forecast, by End User
- 8.5.6.2. Middle East
- 8.5.6.2.1. Key market trends, growth factors and opportunities
- 8.5.6.2.2. Market size and forecast, by Offering
- 8.5.6.2.3. Market size and forecast, by Deployment Mode
- 8.5.6.2.4. Market size and forecast, by Application
- 8.5.6.2.5. Market size and forecast, by End User
- 8.5.6.3. Africa
- 8.5.6.3.1. Key market trends, growth factors and opportunities
- 8.5.6.3.2. Market size and forecast, by Offering
- 8.5.6.3.3. Market size and forecast, by Deployment Mode
- 8.5.6.3.4. Market size and forecast, by Application
- 8.5.6.3.5. Market size and forecast, by End User
CHAPTER 9: COMPETITIVE LANDSCAPE
- 9.1. Introduction
- 9.2. Top winning strategies
- 9.3. Product Mapping of Top 10 Player
- 9.4. Competitive Dashboard
- 9.5. Competitive Heatmap
- 9.6. Top player positioning, 2021
CHAPTER 10: COMPANY PROFILES
- 10.1. AttackIQ.
- 10.1.1. Company overview
- 10.1.2. Key Executives
- 10.1.3. Company snapshot
- 10.1.4. Operating business segments
- 10.1.5. Product portfolio
- 10.1.6. Key strategic moves and developments
- 10.2. Cymulate.
- 10.2.1. Company overview
- 10.2.2. Key Executives
- 10.2.3. Company snapshot
- 10.2.4. Operating business segments
- 10.2.5. Product portfolio
- 10.2.6. Key strategic moves and developments
- 10.3. FireMon, LLC.
- 10.3.1. Company overview
- 10.3.2. Key Executives
- 10.3.3. Company snapshot
- 10.3.4. Operating business segments
- 10.3.5. Product portfolio
- 10.3.6. Key strategic moves and developments
- 10.4. Keysight Technologies
- 10.4.1. Company overview
- 10.4.2. Key Executives
- 10.4.3. Company snapshot
- 10.4.4. Operating business segments
- 10.4.5. Product portfolio
- 10.4.6. Business performance
- 10.4.7. Key strategic moves and developments
- 10.5. Qualys, Inc.
- 10.5.1. Company overview
- 10.5.2. Key Executives
- 10.5.3. Company snapshot
- 10.5.4. Operating business segments
- 10.5.5. Product portfolio
- 10.5.6. Business performance
- 10.5.7. Key strategic moves and developments
- 10.6. Rapid7
- 10.6.1. Company overview
- 10.6.2. Key Executives
- 10.6.3. Company snapshot
- 10.6.4. Operating business segments
- 10.6.5. Product portfolio
- 10.6.6. Business performance
- 10.6.7. Key strategic moves and developments
- 10.7. SafeBreach Inc.
- 10.7.1. Company overview
- 10.7.2. Key Executives
- 10.7.3. Company snapshot
- 10.7.4. Operating business segments
- 10.7.5. Product portfolio
- 10.7.6. Key strategic moves and developments
- 10.8. Skybox Security, Inc.
- 10.8.1. Company overview
- 10.8.2. Key Executives
- 10.8.3. Company snapshot
- 10.8.4. Operating business segments
- 10.8.5. Product portfolio
- 10.8.6. Key strategic moves and developments
- 10.9. Sophos Ltd.
- 10.9.1. Company overview
- 10.9.2. Key Executives
- 10.9.3. Company snapshot
- 10.9.4. Operating business segments
- 10.9.5. Product portfolio
- 10.9.6. Key strategic moves and developments
- 10.10. XM Cyber
- 10.10.1. Company overview
- 10.10.2. Key Executives
- 10.10.3. Company snapshot
- 10.10.4. Operating business segments
- 10.10.5. Product portfolio