|
市場調査レポート
商品コード
1690161
ネットワーク暗号化- 市場シェア分析、産業動向・統計、成長予測(2025年~2030年)Network Encryption - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2025 - 2030) |
||||||
カスタマイズ可能
適宜更新あり
|
|||||||
| ネットワーク暗号化- 市場シェア分析、産業動向・統計、成長予測(2025年~2030年) |
|
出版日: 2025年03月18日
発行: Mordor Intelligence
ページ情報: 英文 120 Pages
納期: 2~3営業日
|
全表示
- 概要
- 目次
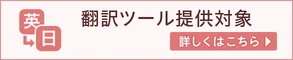
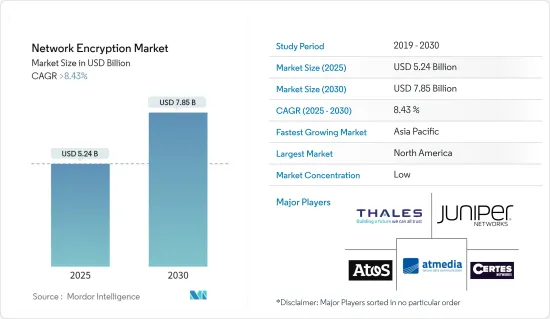
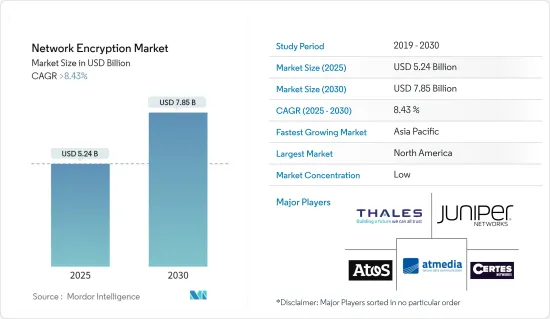
ネットワーク暗号化市場規模は、2025年に52億4,000万米ドルと推定され、予測期間(2025~2030年)のCAGRは8.43%を超え、2030年には78億5,000万米ドルに達すると予測されます。
ネットワーク暗号化の成長は、主に組織におけるデータセキュリティとプライバシーへの関心の高まりに起因しています。
主要ハイライト
- インターネットの成長、クラウドコンピューティング、サイバー攻撃の増加により、より安全なデータ通信とストレージの必要性が高まっています。さらに、一般データ保護規則(GDPR)やペイメントカード産業データセキュリティ基準(PCI DSS)などの政府規制の増加により、組織は安全なデータ伝送方法を導入する必要があり、ネットワーク暗号化の成長をさらに促進しています。
- さらに、さまざまなエンドユーザー産業がモノのインターネット(IoT)ベースのソリューションを業務に採用するようになったことで、IoTネットワーク上で伝送されるデータを保護するための暗号化のニーズが高まり、市場の成長を支えています。
- ネットワーク暗号化産業が成長したのは、新しい暗号化アルゴリズムやより優れた暗号化ソフトウェアが作られたからです。例えば、量子コンピュータが従来の暗号化手法を破る可能性があるため、量子コンピュータが破れない暗号化アルゴリズムを使用することが重要になってきています。
- 暗号化ソリューションの導入は、特にITリソースの少ない企業にとっては、困難で高価なものになる可能性があります。組織によっては、暗号化ソリューションの購入や設定、使用や保守のためのスタッフのトレーニングにかかるコストが、暗号化ソリューションを使用しない理由になることもあります。また、暗号化アルゴリズムによっては、技術的な問題があり、企業ネットワークに適さないものもあります。このような課題が、予測期間中の市場成長の課題となることが予想されます。
- 市場の成長に影響を与える最も重要な要因は、ネットワークセキュリティ侵害の増加、多くの組織によるクラウド技術の利用の増加、より良いデータ保護のために刻々と変化する規制基準を満たす必要性の高まりです。
- COVID-19の流行はネットワーク暗号化市場に大きな影響を与えました。在宅勤務の傾向が強まるにつれ、安全なリモートワークソリューションに対する需要が高まりました。在宅勤務の増加に伴い、企業の機密データを保護するために、安全で信頼性の高い仮想プライベートネットワーク(VPN)やリモートデスクトップソリューションが必要とされました。このため、ネットワーク暗号化製品やサービスの需要が急増し、産業の成長を後押ししました。さらに、パンデミックに関連したサイバー攻撃やセキュリティ侵害の増加に対処するため、企業はサイバーセキュリティへの投資を増加させました。
ネットワーク暗号化市場の動向
電気通信・ITセグメントが市場で大きなシェアを占める見込み
- 世界のIT・通信産業がネットワーク暗号化を推進する主要因としては、クラウド利用の拡大、光通信への投資の増加、ネットワークデータ漏えいの増加、政府の厳しい規制などが挙げられます。
- さらに、プライベートネットワークの採用拡大、ネットワーク自動化の動向、5Gネットワークの展開により、ネットワークトラフィックが大幅に増加し、より先進的セキュリティ対策が必要になると予想されます。ネットワークの暗号化は、これらのネットワーク上で機密データの安全を守り、新たなビジネス機会を開くことになります。
- VIAVISIONによると、2023年4月現在、5Gネットワークへのアクセスが最も多いのは米国の503都市で、356都市で5Gが利用可能な中国が2位に続いています。
- スマート工場、インテリジェント交通システム、第5世代以降の携帯電話ネットワーク、モノのインターネット、分散型台帳技術、量子安全通信などの新たなICT技術には、様々な脅威やリスクに対処するための技術的・組織的対策が必要です。
- 5G技術の導入により、ネットワークに接続されるモノのインターネット(IoT)デバイスはおそらく増加し、ハッカーがより広範で巧妙な攻撃を行う新たな機会が広がります。Ericssonによると、モバイルデータトラフィックの総量は2023年の月間26EBから2029年には月間73EBに増加し、CAGR19%で成長すると予想されています。これらすべての要因が、通信ベンダーのネットワーク自動化の範囲を拡大し、調査市場の需要を煽っています。
- さらに、世界のセキュリティサービスの革新的拡大や採用が、ネットワーク暗号化技術の需要をさらに押し上げています。通信に対する脅威は、レガシー技術を持つ産業における典型的なIPベースの脅威の組み合わせに起因します。5G技術が進歩するにつれ、脅威の表面は拡大し、攻撃者はより多くの機会を得ることになります。このため、通信会社のサイバーセキュリティチームは、新たな脅威やトリアージすべきアラートの増加に直面しながらも、攻撃者の一歩先を行くために、新しい技術や自動化を活用してワークフローを合理化する方法を模索しています。
北米が大きな市場シェアを占める見込み
- 北米は、技術的に設備の整った地域です。米国やカナダのような新興経済諸国が大きな市場シェアを占めており、あらゆる規模の企業が政府の規則や規制に従うための適切なプラットフォームが整っています。
- 北米政府は、機密データを転送中に保護することを求める規則を設けています。このため、こうした規制要件を満たすネットワーク暗号化ソリューションの必要性が高まっている
- さらに2023年9月、量子安全暗号の世界的リーダーの1つであるArqit Quantum Inc.と、デジタルインフラ向けの世界の信頼されるサイバーセキュリティのスペシャリストであるExclusive Networks North Americaは、Arqit独自の対称鍵合意プラットフォームに関する合意を発表しました。Joining Networksのベンダーとチャネルパートナーのポートフォリオは、量子コンピューティングによるリスクを含む現在と将来のサイバー脅威から保護するArqitの技術を提供することができます。
- この地域のハイテク産業が成長を続けるにつれ、ネットワーク暗号化ソリューションに対する需要が高まっています。これは、クラウドコンピューティングが普及し、企業がクラウドとの間で機密データを送受信する際に保護したいと考えるようになったためです。企業はまた、ネットワークを暗号化するためのより先進的方法を開発するための研究開発にも資金を費やしています。こうした投資が産業の成長に寄与しています。
- 最近改正されたEARN IT法が成立すれば、強力な暗号化は不安定な地盤に置かれることになるが、暗号化データへの合法的アクセス法(LAEDA)は、何百万人もの人々が個人と国家の安全保障のために毎日利用しているツールを直接攻撃するものです。
ネットワーク暗号化産業概要
ネットワーク暗号化市場は細分化されており、複数の参入企業が活動しています。同市場で大きなシェアを持つ大手企業は、市場シェアと収益性を高めるために戦略的協業イニシアティブを活用し、海外における顧客基盤の拡大に注力しています。Thales Trusted Cyber Technologies、Atos SE、Juniper Networks, Inc.、Certes Networks, Inc.、Senetas Corporation Ltd.、Viasat Inc.、Raytheon Technologies Corporation、Securosys SA.、Packetlight Networksは、現在の市場に存在し、合併、買収、コラボレーション、製品革新などの戦略的イニシアチブを取っている主要企業の一部です。
2023年2月、Atosは、プライベート5Gネットワークの導入を検討している企業や、統合された自動化を実現しようとしている通信事業者向けに、新しい「5Guard」セキュリティの提供を開始すると発表しました。これらの企業は、資産と顧客を保護・防御するために、セキュリティのオーケストレーションを行っています。Atosの製品ポートフォリオには、Atosの暗号化ソリューション(Trustway)、ID・アクセス管理ソフトウェア、公共重要インフラソリューション(IDnomic)、Atos Managed Detection and Response(MDR)プラットフォームがあり、潜在的な脅威をほぼリアルタイムで検知・対応することで、5Gネットワーク要素、アプリケーション、ワークロードのセキュリティを向上させています。
2023年1月、デジタルインフラを製造するEquinixは、クラウドサービスを製造するアヴィアトリクスと協力し、企業環境向けの高性能暗号化を実現しました。この提携により、Aviatrix Edgeソフトウェアは、Equinixの世界25カ所以上のビジネス交流データセンターで利用できるようになります。EquinixのNetwork EdgeとEquinix Fabricを利用したこのソリューションの組み合わせにより、クラウドへの最も高速で安全な接続が実現し、複数のクラウドで何が起きているかを確認することができます。
その他の特典
- エクセル形式の市場予測(ME)シート
- 3ヶ月間のアナリストサポート
目次
第1章 イントロダクション
- 調査の前提条件と市場定義
- 調査範囲
第2章 調査手法
第3章 エグゼクティブサマリー
第4章 市場洞察
- 市場概要
- 産業の魅力-ポーターのファイブフォース分析
- 供給企業の交渉力
- 買い手の交渉力
- 新規参入業者の脅威
- 代替品の脅威
- 競争企業間の敵対関係の強さ
- COVID-19の市場への影響評価
第5章 市場力学
- 市場の促進要因
- ネットワークセキュリティ侵害の増加
- 多数の組織によるクラウド技術の採用増加
- 市場課題
- ネットワーク暗号化ソリューションの導入コストの高さ
第6章 市場セグメンテーション
- 導入タイプ別
- クラウド
- オンプレミス
- コンポーネント別
- ハードウェア
- ソリューション&サービス
- 組織規模別
- 中小企業
- 大企業
- エンドユーザー産業別
- 通信・IT
- BFSI
- 政府機関
- メディア&エンターテイメント
- その他
- 地域別
- 北米
- 欧州
- アジア太平洋
- ラテンアメリカ
- 中東・アフリカ
第7章 競合情勢
- 企業プロファイル
- Thales Trusted Cyber Technologies
- ATMedia Gmbh
- Atos SE
- Juniper Networks Inc.
- Certes Networks Inc.
- Senetas Corporation Ltd.
- Viasat Inc.
- Raytheon Technologies Corporation
- Securosys SA
- Packetlight Networks
- Rohde & Schwarz Cybersecurity GmbH
- Colt Technology Services Group Ltd.
- Ciena Corporation
第8章 投資分析
第9章 市場の将来
The Network Encryption Market size is estimated at USD 5.24 billion in 2025, and is expected to reach USD 7.85 billion by 2030, at a CAGR of greater than 8.43% during the forecast period (2025-2030).
The growth of network encryption is primarily attributed to the increasing concern for data security and privacy in organizations.
Key Highlights
- The growth of the internet, cloud computing, and the increasing number of cyberattacks have led to the need for more secure data communication and storage. Additionally, increasing government regulations, such as the General Data Protection Regulation (GDPR) and the Payment Card Industry Data Security Standard (PCI DSS), require organizations to implement secure data transmission methods, further driving the growth of network encryption.
- Furthermore, the growth in adopting Internet of Things (IoT)-based solutions by the various end-user industries in their operations has increased the need for encryption to secure data transmitted over IoT networks, supporting market growth.
- The network encryption industry has grown because new encryption algorithms and better encryption software have been made. For example, using encryption algorithms that quantum computers can't break is becoming more important because quantum computers could break traditional encryption methods.
- Putting encryption solutions into place can be hard and expensive, especially for businesses with few IT resources. For some organizations, the cost of buying and setting up encryption solutions and training staff to use and maintain them can be a reason not to use them. Also, some encryption algorithms may have technical problems that make them unsuitable for s networks. Such factors are expected to challenge the market's growth during the forecast period.
- The most important factors affecting the market's growth are the growing number of network security breaches, the increasing use of cloud technologies by many organizations, and the growing need to meet ever-changing regulatory standards for better data protection.
- The COVID-19 pandemic significantly affected the network encryption market. As the trend toward working from home grew, there was more demand for secure remote work solutions. With more people working from home, there was a need for secure and reliable virtual private networks (VPNs) and remote desktop solutions to protect sensitive corporate data. This led to a surge in demand for network encryption products and services, boosting growth in the industry. Additionally, businesses increased their investment in cybersecurity to address the rise in cyber-attacks and security breaches related to the pandemic.
Network Encryption Market Trends
Telecom and IT Sector is Expected to Hold a Significant Share of the Market
- Some of the main things pushing the IT and telecom industries worldwide to use network encryption are the growing use of the cloud, increasing investment in optical communication, growing network data breaches, and strict government regulations.
- Furthermore, the growing adoption of a private network, trends in network automation, and the rollout of 5G networks are expected to significantly increase network traffic, requiring more advanced security measures. Network encryption will keep sensitive data safe on these networks, opening up new business opportunities.
- According to VIAVISION, as of April 2023, with the highest 5G network access, it was available in 503 cities in the United States; with 5G availability in 356 cities, China followed in second.
- Emerging ICT technologies such as smart factories, intelligent transportation systems, the 5th generation of cellular networks and beyond, the Internet of Things, distributed ledger technologies, and quantum-safe communication need technical and organizational measures to address various threats and risks.
- The deployment of 5G technology will probably lead to increased Internet of Things (IoT) devices connected to networks, opening up new chances for hackers to conduct more extensive and sophisticated assaults. According to Ericsson, Total mobile data traffic is expected to grow from 26 EB per month in 2023 to 73 EB per month in 2029, growing at a CAGR of 19 percent. All these factors are expanding the scope of network automation among telecom vendors, fueling the demand in the studied market.
- Furthermore, the innovation expansion launch and adoption of security services across the globe have further boosted the demand for network encryption techniques. Threats against telecommunications result from a combination of typical IP-based threats in an industry with legacy technology. As 5G technology advances, the threat surface will only expand, giving attackers more opportunities. This leaves cybersecurity teams at telecom companies looking for ways to leverage new technology and automation to streamline workflows to stay ahead of attackers in the face of new threats and an increasing number of alerts to triage.
North America is Expected to Hold Significant Market Share
- North America is a well-equipped region in terms of technology. It has a significant market share because of developed economies like the United States and Canada, and it has the right platforms for businesses of all sizes to follow government rules and regulations.
- The government of North America has put in place rules that require sensitive data to be protected while in transit. This has driven the need for network encryption solutions to meet these regulatory requirements.
- Furthermore, in September 2023, Arqit Quantum Inc., one of the global leaders in quantum-safe encryption, and Exclusive Networks North America, a global trusted cybersecurity specialist for digital infrastructure, announced an agreement for Arqit's unique Symmetric Key Agreement Platform. Joining Networks' portfolio of vendors and channel partners can provide Arqit's technology that protects against current and future cyber threats, including the risk from quantum computing.
- As the tech industry in the region continues to grow, there is more demand for network encryption solutions. This is because cloud computing is becoming more popular, and organizations want to protect sensitive data while it is being sent to and from the cloud. The companies also spend money on research and development to develop more advanced ways to encrypt networks. This investment is contributing to the growth of the industry.
- While the recently amended EARN IT Act would leave strong encryption on unstable ground if passed into law, The Lawful Access to Encrypted Data Act (LAEDA) is a direct assault on the tool millions of people rely on for personal and national security each day.
Network Encryption Industry Overview
The network encryption market is fragmented, with several players operating. The major players with a prominent share in the market are focusing on expanding their customer base across foreign countries by leveraging strategic collaborative initiatives to increase their market share and profitability. Thales Trusted Cyber Technologies, Atos SE, Juniper Networks, Inc., Certes Networks, Inc., Senetas Corporation Ltd., Viasat Inc., Raytheon Technologies Corporation, Securosys SA., and Packetlight Networks are some of the major players present in the current market and undergoing strategic initiatives such as mergers, acquisitions, collaboration, product innovation, and others.
In February 2023, Atos announced the launch of its new '5Guard' security offering for organizations looking to deploy private 5G networks and for telecom operators looking to enable integrated, automated. They orchestrated security to protect and defend their assets and customers. Atos'product portfolio is Atos'encryption solutions (Trustway), identity and access management software; public critical infrastructure solutions (IDnomic); and Atos Managed Detection and Response (MDR) platform that elevates the security of 5G network elements, applications, and workloads by detecting and responding to potential threats in near real-time.
In January 2023, Equinix, a company that makes digital infrastructure, worked with Aviatrix, which makes cloud services, to make high-performance encryption for enterprise environments. This partnership will make the Aviatrix Edge software available in over 25 of Equinix's global business exchange data centers. The combined solution, which uses Equinix's Network Edge and Equinix Fabric, gives you the fastest, most secure connection to the cloud to see what's happening in multiple clouds.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET INSIGHTS
- 4.1 Market Overview
- 4.2 Industry Attractiveness - Porter's Five Forces Analysis
- 4.2.1 Bargaining Power of Suppliers
- 4.2.2 Bargaining Power of Buyers
- 4.2.3 Threat of New Entrants
- 4.2.4 Threat of Substitute Products
- 4.2.5 Intensity of Competitive Rivalry
- 4.3 Assessment of the Impact of COVID-19 on the Market
5 MARKET DYNAMICS
- 5.1 Market Drivers
- 5.1.1 Increasing Number of Network Security Breaches
- 5.1.2 Increasing Adoption of Cloud Technologies by Numerous Organizations
- 5.2 Market Challenges
- 5.2.1 High Implementation Cost of Network Encryption Solutions
6 MARKET SEGMENTATION
- 6.1 By Deployment Type
- 6.1.1 Cloud
- 6.1.2 On-premise
- 6.2 By Component
- 6.2.1 Hardware
- 6.2.2 Solutions & Services
- 6.3 By Organization Size
- 6.3.1 Small and Medium-sized Enterprises
- 6.3.2 Large-sized Enterprises
- 6.4 By End-user Industry
- 6.4.1 Telecom & IT
- 6.4.2 BFSI
- 6.4.3 Government
- 6.4.4 Media & Entertainment
- 6.4.5 Other End-user Industries
- 6.5 By Geography
- 6.5.1 North America
- 6.5.2 Europe
- 6.5.3 Asia Pacific
- 6.5.4 Latin America
- 6.5.5 Middle East and Africa
7 COMPETITIVE LANDSCAPE
- 7.1 Company Profiles
- 7.1.1 Thales Trusted Cyber Technologies
- 7.1.2 ATMedia Gmbh
- 7.1.3 Atos SE
- 7.1.4 Juniper Networks Inc.
- 7.1.5 Certes Networks Inc.
- 7.1.6 Senetas Corporation Ltd.
- 7.1.7 Viasat Inc.
- 7.1.8 Raytheon Technologies Corporation
- 7.1.9 Securosys SA
- 7.1.10 Packetlight Networks
- 7.1.11 Rohde & Schwarz Cybersecurity GmbH
- 7.1.12 Colt Technology Services Group Ltd.
- 7.1.13 Ciena Corporation