
コンテナセキュリティ:市場シェア分析、産業動向、統計、成長予測(2025年~2030年)
Container Security - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2025 - 2030)- 発行日
- ページ情報
- 英文 137 Pages
- 納期
- 2~3営業日
- 商品コード
- 1851101
- カスタマイズ可能 お客様のご希望に応じて、既存データの加工や未掲載情報(例:国別セグメント)の追加などの対応が可能です。詳細はお問い合わせください。
- 適宜更新あり 本レポートは最新情報反映のため適宜更新し、内容構成変更を行う場合があります。ご検討の際はお問い合わせください。
- 翻訳ツール提供対象 PDF対応AI翻訳ツールの無料貸し出しサービスのご利用が可能です
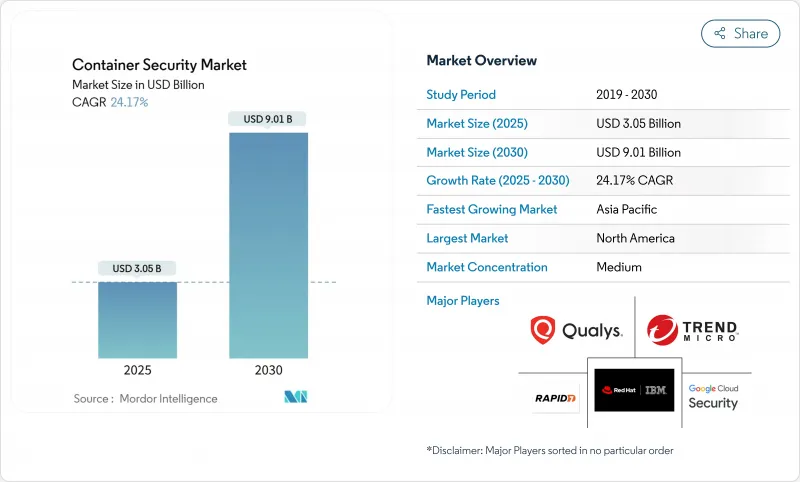
コンテナセキュリティの市場規模は2025年に30億5,000万米ドルと推計され、2030年には90億1,000万米ドルに拡大すると予測されています。
絶え間ない成長は、モノリシックなソフトウェアから、複数のクラウドやエッジサイトにまたがるクラウドネイティブなコンテナ化アーキテクチャへの移行を反映しています。組織は現在、従来の境界防御ではなく、アプリケーションとともに移動するゼロトラスト、ワークロード中心の制御を好んでいます。アジア太平洋企業の53%はすでにコンテナを実運用しており、クラウド間で一貫性のないセキュリティ態勢が重要なワークロードを暴露していることを認識しているため、需要はさらに加速しています。また、PCI-DSS 4.0、NIS2、ソフトウェア部品表(SBOM)の開示など、法規制に対する関心の高まりにより、コンテナセキュリティは裁量的な投資からコンプライアンスの必須条件へと変化しています。これと並行して、5Gやエッジ・プラットフォームの急速な展開により、コンテナ化されたネットワーク機能が導入され、新たな攻撃対象が生まれ、特殊なランタイム・セーフガードが必要になります。持続的なベンチャー企業の資金調達と記録的な規模の買収は、2025年3月にグーグルが320億米ドルでWizを買収したことに代表されるように、クラウドネイティブ保護の戦略的役割を強調しています。
世界のコンテナセキュリティ市場の動向と洞察
ハイブリッドおよびマルチクラウド・コンテナ・ワークロードの採用増加
企業は、コストと耐障害性を最適化するために、2つ以上のパブリッククラウド上でワークロードを同時に運用していますが、セキュリティ管理、API、コンプライアンス義務に一貫性がないため、可視性のギャップがリスクを高めています。ABN AMROのような金融機関は、複数のクラウドにまたがるHashiCorp Vaultで秘密を一元管理し、プラットフォームにとらわれない制御が、導入の選択肢を維持しながらポリシーを統一することを実証しています。セキュリティベンダーは現在、すべてのクラスターを検出し、ポリシーを標準化し、コンプライアンスの証拠収集を自動化するオーケストレーションレイヤーを出荷しています。マルチクラウドの複雑さが孤立したツールの利点を上回ったため、統合ダッシュボードとエージェントレスディスカバリの需要が高まり続けています。
マイクロサービスとDevSecOpsパイプラインへの急速なシフト
大規模アプリケーションを数百の疎結合サービスに分割することで、リリースの速度は向上するが、継続的インテグレーションと継続的デプロイのフロー全体にセキュリティチェックが挿入されます。小売企業のTarget社は、Unimatrixプラットフォームを通じて毎週何百ものアップデートを展開する一方で、自動スキャンとポリシーゲートを組み込み、脆弱なイメージが本番環境に到達するのを防いでいます。セキュリティプラットフォームは、一般的なCI/CDツールのネイティブプラグインを公開し、ポリシーアズコードテンプレートを有効にし、実行前に設定ミスを自動修正するようになってきています。
DevOpsチームにおけるコンテナセキュリティのスキルセットの不足
Kubernetesに精通したセキュリティエンジニアの需要は供給を上回っており、特に新興国では大学がまだ専門カリキュラムを展開していないです。企業は、スタッフの学習曲線がプロジェクトを遅らせるため、デプロイサイクルが長くなると報告しています。ベンダーは現在、処方的ポリシーテンプレート、AIチャットアシスタント、マネージド検出サービスをバンドルして専門知識のギャップを縮小しているが、人材不足は引き続き展開速度を低下させています。
セグメント分析
2024年の売上高の72.1%をソフトウェアが占め、オーケストレーションレイヤーに直接組み込まれた自動スキャン、ポリシーエンジン、ランタイム検知への需要が浮き彫りになりました。しかし、多くの企業がアーキテクチャの設計、パイプラインの統合、24時間365日のモニタリングの実行に外部の専門家を必要としているため、プロフェッショナルサービスおよびマネージドサービスのCAGRは24.7%で成長しています。コンサルティング契約は通常、ハイブリッド・エステート全体の秘密管理、ネットワーク・マイクロセグメンテーション、コンプライアンス・マッピングに対応しています。
サービスの波は、顧客が社内にスタッフを配置できない管理業務を専門家パートナーに任せることで、プラットフォームの消費を増幅させる。Kubernetes、コンテナレジストリ、サービスメッシュをカバーするマネージド検出サービスは、リソースに制約のあるチームを緩和し、コンテナセキュリティ市場への浸透を促進します。また、この動向は、本番ワークロードを投入する前に文書化された運用ランブックを求める規制産業における対応可能な裾野を広げます。
大企業は、大規模なIT資産とフルスタック保護を要求する規制上の義務により、2024年に65.6%のシェアを維持します。これらの顧客は、ポリシーアズコード、自動化されたコンプライアンスエビデンス、ディープパケットインスペクションをマイクロサービスのワークフローに直接組み込み、成熟したセキュリティ体制を反映しています。
中堅・中小企業は、消費ベースの価格設定によって複雑さを隠蔽し、簡素化されたクラウド提供製品によって、CAGR 25.3%で拡大しています。ベンダーは現在、スキャン、シークレットローテーション、基本的なランタイムガードレールを単一のダッシュボードにバンドルしており、中小企業は専任のSOCスタッフがいなくてもコンテナを導入できます。カスペルスキーのコンテナセキュリティのようなソリューションは、ガバナンスを維持しながら地理的な拡大を追求する分散チームに対応し、リソースに制約のある組織におけるコンテナセキュリティ市場の浸透を拡大します。
地域分析
北米は、Kubernetesの早期導入、高いサイバー成熟度、連邦政府のゼロトラスト指令の恩恵を受け、2024年の売上高が28.9%を占めました。GoogleによるWizの買収のような画期的な取引は、コンテナ保護をより広範なクラウドプラットフォームに緊密に統合することを目的とした継続的な統合を示唆しています。金融サービス、防衛、テクノロジーの各業界は、FIPS準拠の暗号やマルチクラスターフェデレーションなどの機能を引き続き形成しています。
アジア太平洋地域は、CAGR24.3%で最も急速に拡大しています。デジタルイニシアティブ、政府によるクラウド政策の支援、開発者コミュニティの拡大により、コンテナの展開が加速しており、この地域の企業の53%はすでに本番稼動しています。通信事業者は5Gエッジノードを活用し、製造企業はスマートファクトリーの青写真を採用することが、この地域の成長にとって極めて重要です。サイバーインシデントの増加も、脅威インテリジェンスの自動フィードやマネージド検知サービスへの支出を後押ししています。
欧州は厳格なデータ保護法を背景に大きなシェアを維持しています。NIS2指令は、約35万の組織にコンテナ・オーケストレーション防御の強化を促し、ガバナンスを重視したコントロールと継続的なコンプライアンス監査の需要を高めています。金融機関は、マルチクラウドの俊敏性とプライバシーの義務を調和させるために、HashiCorp Vaultのような一元化された秘密管理ツールに依存しています。このような力学は、大陸全体におけるコンテナセキュリティ市場の着実な拡大を保証しています。
その他の特典:
- エクセル形式の市場予測(ME)シート
- 3ヶ月間のアナリストサポート
よくあるご質問
目次
第1章 イントロダクション
- 調査の前提条件と市場の定義
- 調査範囲
第2章 調査手法
第3章 エグゼクティブサマリー
第4章 市場情勢
- 市場概要
- 市場促進要因
- ハイブリッドおよびマルチクラウド・コンテナ・ワークロードの採用増加
- マイクロサービスとDevSecOpsパイプラインへの急速なシフト
- セキュリティの義務化(PCI-DSS 4.0、NIS2、SBOMなど)
- コンテナイメージに対するサプライチェーン攻撃の頻度上昇
- エッジと5Gコンテナランタイムの普及
- ハードウェアレベルのコンテナ隔離イノベーション
- 市場抑制要因
- DevOpsチームにおけるコンテナセキュリティのスキルセットの不足
- マルチクラウド、マルチクラスターエステートの運用の複雑性
- アラート疲労と偽陽性過多
- 高度なコンテナ・エスケープ・キルチェーン
- サプライチェーン分析
- 規制情勢
- テクノロジーの展望
- ポーターのファイブフォース分析
- 供給企業の交渉力
- 買い手の交渉力
- 新規参入業者の脅威
- 代替品の脅威
- 競争企業間の敵対関係
第5章 市場規模と成長予測
- コンポーネント別
- プラットフォーム/ ソフトウェア
- サービス
- 企業規模別
- 大企業
- 中小企業
- 展開別
- クラウドベース
- オンプレミス
- セキュリティ・コントロール別
- 画像スキャンと脆弱性管理
- ランタイム保護と異常検知
- コンプライアンスとコンフィギュレーション管理
- エンドユーザー業界別
- ITおよび電気通信
- BFSI
- 小売とeコマース
- ヘルスケアとライフサイエンス
- 工業および製造業
- その他(メディア、教育、政府機関)
- 地域別
- 北米
- 米国
- カナダ
- メキシコ
- 南米
- ブラジル
- アルゼンチン
- その他南米
- 欧州
- ドイツ
- 英国
- フランス
- イタリア
- スペイン
- その他欧州地域
- アジア太平洋地域
- 中国
- 日本
- インド
- 韓国
- オーストラリア
- その他アジア太平洋地域
- 中東・アフリカ
- 中東
- サウジアラビア
- アラブ首長国連邦
- トルコ
- その他中東
- アフリカ
- 南アフリカ
- ナイジェリア
- エジプト
- その他アフリカ
- 北米
第6章 競合情勢
- 市場集中度
- 戦略的動向
- 市場シェア分析
- 企業プロファイル
- Google Cloud Security
- Red Hat(IBM)
- Trend Micro
- Qualys
- Rapid7
- Suse NeuVector
- Mirantis
- Thales
- Sysdig
- Anchore
- Prisma Cloud by Palo Alto
- Tenable
- AccuKnox
- Tigera
- VMware(NSX-ALB)
- Microsoft Defender for Containers
- Capsule8(Snowflake)
- Fidelis Cybersecurity
第7章 市場機会と将来の展望
- 発行日
- 発行
- Mordor Intelligence
- ページ情報
- 英文 137 Pages
- 納期
- 2~3営業日